【2015/07/08】International Workshop on Cybersecurity
International Workshop on Cybersecurity
―― System Design and Business with Advanced Cybersecurity Technology

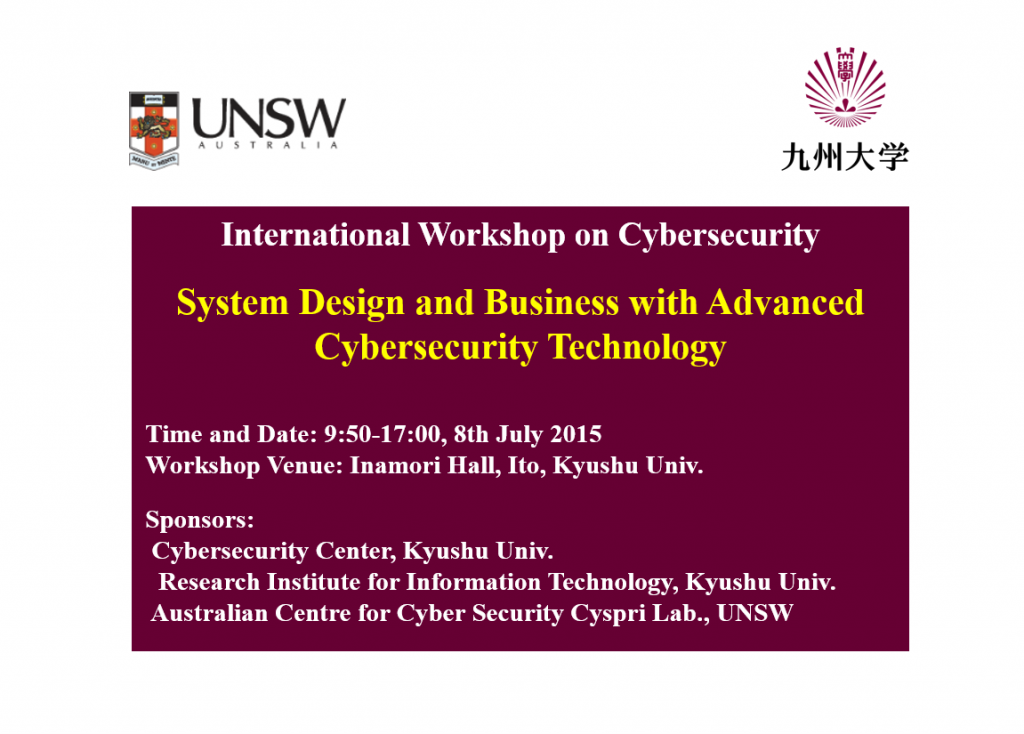
International Workshop on Cybersecurity
System Design and Business with Advanced Cybersecurity Technology
| 9:50 | Opening |
| 10:00-12:00 | Session 1: Cybersecurity Technology |
| 12:00-13:00 | Lunch Break |
| 13:00-14:50 | Session 2: Security-Aware System Design |
| 14:50-15:10 | Afternoon Break |
| 15:10-17:00 | Session 3: Cyber Security, Business, Society, and the Future |
| 17:00 | Closing |
| Dinner |
Workshop Venue: Inamori Hall
http://www.inamori-center.kyushu-u.ac.jp
Program
Opening
Koji OKAMURA (Director of Cybersecurity Center)
Chair: Hidenobu Watanabe
| 1. Introduction of some joint projects about information gathering and building cooperation system against cyber attacks | Koichi Sakurai (Faculty of Information Science and Electrical Engineering/Cybersecurity Center) |
| 2. Security Evaluation of Next-Generation Cryptography | Tsuyoshi Takagi (Institute of Mathematics for Industry/Cybersecurity Center) |
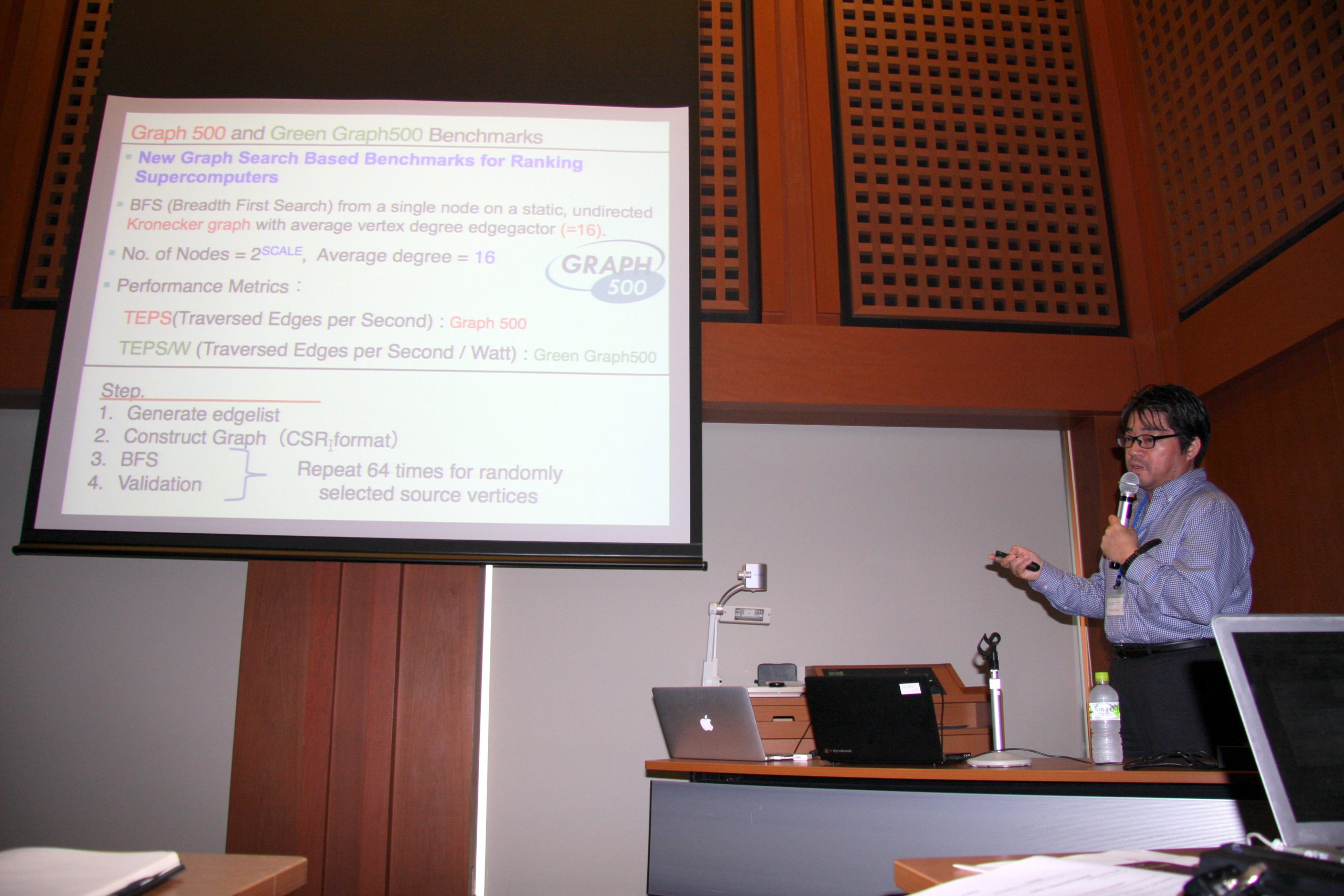
| 3. Large-Scale Graph Analysis for Cyber Security on Post Peta-Scale Supercomputers | Katsuki Fujisawa (Institute of Mathematics for Industry/Cybersecurity Center) |
| 4. Crowd sourcing for security | Boualem Benatallah (Cyspri, UNSW) |
| 5. ProfileGuard: Privacy Preserving Obfuscation for Mobile User Profiles | Salil Kanhere (Cyspri, UNSW) |
Lunch Break
Chair: Koji Inoue (Faculty of Information Science and Electrical Engineering)
| 1. Design for Endpoint Devices Considering Security | Mikio Hashimoto (Computer Architecture and Security Systems Laboratory Corporate R & D Center, Toshiba Corp.) |
| 2. Journey through the vehicle security landscape | Dennis Kengo Oka (ESCRYPT, Embedded Security, ETAS K.K.) |
| 3. IoT, CPS, and security issues of Embeded devices | Yasuyoshi Uemura (ECSEC.TRA President, Chiyoda Platform Square) |
| 4. Three Attacks, Many Process Variations and One Expansive Countermeasure | Sri Parameswaran(Cyspri, UNSW) |
Chair: Toshiya Jitsuzumi (Faculty of Economics/Cybersecurity Center)
| 1. A Changing Landscape: Securing the Internet of Things (IoT) | Sanjay Jha (Cyspri, UNSW) |
Panel Discussion
Discussion Theme
1. What is the basic “cybersecurity literacy” of the society, mainly for non-engineer users, how to attain it, and what is the role of universities?
2. Do you think that an economic incentive to improve cybersecurity is sufficient for firms? If yes, how do you explain the recent problems? If no, what should the society do?
| 2. Social Acceptance of Technology Related Risks | Masanori Kusunoki (Executive Advisor to the Government CIO) |
| 3. Threat Information Sharing in Private Sector | Nobukazu Matake (GREE) |
| 4. ybersecurity Strategy in Japan and Public Private Cooperation | Haruo Takasaki(KDDI Research Institute) |
Closing
Rin-ichiro Taniguchi (Director of Research Institute for Information Technology)
Abstract of each talk
Crowd sourcing for security
Boualem Benatallah
Crowd-sourcing harnesses the wisdom of large groups and communities working independently to solve problems, much as open source does for software development. From a service customer’s perspective, crowd-sourcing is a form of digital service (notwithstanding its essentially human infrastructure), yet its unique value is that it is an effective way to perform tasks that remain difficult for, or even beyond the reach of, machine computation: image tagging, natural language translation, and transcription, for example. Software security sector exploration of crowd sourcing is embryonic. In this We will discuss critical challenges in the effective use of crowd sourcing in security management tasks (e.g., vulnerability discovery). We will focus on security for Application Programming Interfaces (APIs). We will discuss issues and state of the art regarding security professional selection, task decomposition and quality control.
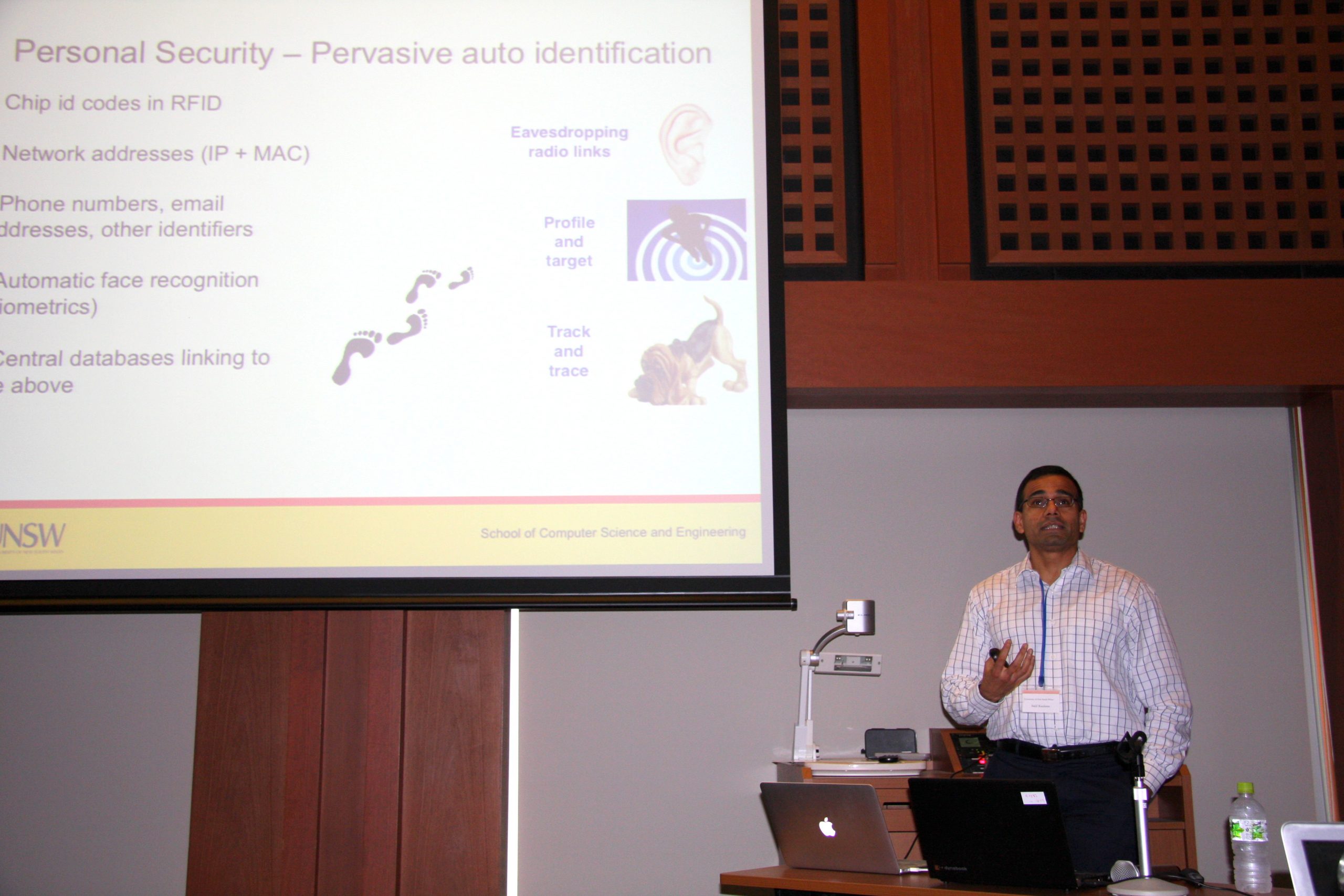
ProfileGuard: Privacy Preserving Obfuscation for Mobile User Profiles
Salil Kanhere
Analytics companies have become an integral part of the mobile advertising industry, enabling successful user targeting via user profiles, derived from the mobile apps installed by specific users. This poses a threat to privacy of such users, when apps indicating sensitive information, e.g., a gaming app showing a gambling problem, are the basis for profiling. In this paper, we propose a ProfileGuard, novel app-based obfuscation mechanism to remove the dominance (prevalence amongst the interest categories present in a user profile) of selected private user profile interest categories. We show, based on extensive experimental evaluation using 2700 Android apps during a 9 month test campaign, that the best trade-off between the level of effort required by the obfuscating system and the resulting privacy protection can be achieved by choosing the obfuscating apps based on similarity with user’s existing apps (while ensuring that the selected apps belong to a non-private category). We implement a proof-of-concept ProfileGuard app to demonstrate the feasibility of an automated obfuscation mechanism. We also provide insights into the broad Google AdMob profiling rules, showing that there is a deterministic mapping of individual apps to profile interests, that profiles based on multiple apps represent a union of individual app profiles and that there is a minimum level of activity necessary for AdMob to build a stable user profile. Finally, we show the resulting effect of obfuscation on the received ads, demonstrating that modifying user profiles to include a richer set of interests results in correspondingly more diverse received ads.
A Changing Landscape: Securing the Internet of Things (IoT)
Sanjay Jha
First part of this talk will discuss how the community is converging towards the IoT vision having worked in wireless sensor networking and Machine-2-Machine (M2M) communication. This will follow a general discussion of security challenges in IoT. Finally I will discuss some results from an ongoing project on security of bodyword devices. Wireless bodyworn sensing devices are becoming popular for fitness, sports training and personalized healthcare applications. Securing the data generated by these devices is essential if they are to be integrated into the current health infrastructure and employed in medical applications. In this talk, I will discuss a mechanism to secure data provenance for these devices by exploiting symmetric spatio-temporal characteristics of the wireless link between two communicating parties. Our solution enables both parties to generate closely matching `link’ fingerprints, which uniquely associate
A data session with a wireless link such that a third party, at a later date, can verify the links the data was communicated on. These fingerprints are very hard for an eavesdropper to forge, lightweight compared to traditional provenance mechanisms, and allow for interesting security properties such as accountability and non-repudiation. I will present our solution with experiments using bodyworn devices in scenarios approximating actual device deployment.
Three Attacks, Many Process Variations and One Expansive Countermeasure
Sri Parameswaran
Deep devastation is felt when privacy is breached, personal information is lost, or property is stolen. Now imagine when all of this happens at once, and the victim is unaware of its occurrence until much later. This is the reality, as increasing amount of electronic devices are used as keys, wallets and files. Security attacks targeting embedded systems illegally gain access to information or destroy information. Advanced Encryption Standard (AES) is used to protect many of these embedded systems. While mathematically shown to be quite secure, it is now well known that AES circuits and software implementations are vulnerable to side channel attacks. Side-channel attacks are performed by observing properties of the system (such as power consumption, electromagnetic emission, etc.) while the system performs cryptographic operations. In this talk, differing power based attacks are described, and various countermeasures are explained. In particular, a countermeasure titled Algorithmic Balancing is described in detail. Implementation of this countermeasure in hardware and software is described. Since process variation impairs countermeasures, we show how this countermeasure can be made to overcome process variations.
Social Acceptance of Technology Related Risks
Masanori Kusunoki, Executive Advisor to the Government CIO, Cabinet Secretariat
楠正憲(内閣官房政府CIO補佐官)
Policy maker faces concern about new technology related risks from public sentiment. it’s difficult to balancing risk/benefit before technology deployment. We need to impress benefit to drive innovation, but social acceptance is key factor to technology deployment and regulation reform. I’d like to discuss about how to promote new technologies and avoid conflict and crime.
Threat Information Sharing in Private Sector
Nobukazu Matake, GREE
真武信和(グリー(株))
Several US private sector organizations are working on a threat information sharing project which enables private sector entities share threat information (account hijacking, security token leakage etc.) with each other. Such information is important to defend against similar attacks to the same user accounts on other services. However it requires sharing PII, thus it can conflict with the privacy protection law. What should we handle such conflict?
Cybersecurity Strategy in Japan and Public Private Cooperation
Haruo Takasaki, KDDI Research Institute
高崎晴夫(㈱KDDI総研 主席研究員)
For strengthening the counter ability against cyber threats, A Cybersecurity Basic Act has been passed in last November 2014. Cybersecurity Strategic Headquarters have been set up and they are developing Cybersecurity Strategy and Policy Plans for facilitating cybersecurity cooperation among multiple stakeholders including the Central and local governments and critical infrastructure provider. Actual status of strategy planning and action items for public private cooperation in this field would be explained in the presentation.
Presentation title: Design for Endpoint Devices Considering Security
Mikio Hashimoto
While rapid prevailing of cloud computing technologies, endpoint device security is also getting more serious. Since networking is applied from home appliance to social infrastructure. In this talk, typical threats and countermeasure technologies on endpoint device security are briefly introduced. Countermeasure for endpoint device includes one against physical attack. In addition, other security related issue such as effects of open development environment will be outlined.
Journey through the vehicle security landscape
Dennis Kengo Oka
岡 デニス 健五 (ESCRYPT – エンベデッドセキュリティ イータス株式会社)
Modern vehicles are equipped with embedded computers responsible for a majority of functionality of the vehicle. These electronic control units (ECUs) handle for example engine control, airbag deployment, and driver assistance systems. Moreover, there is a trend towards the connected car where vehicles are wirelessly interacting with their surroundings such as other vehicles, the infrastructure or owners’ devices. Useful examples include improving safety, reducing traffic congestion and improving user services. Moreover, autonomous driving is on the horizon for many OEMs. Naturally, security is an extremely important aspect as a vehicle that allows wireless interaction also provides a potential entrypoint for an attacker. This talk will take you on a journey through the vehicle landscape discussing relevant security threats and solutions.
IoT, CPS, and security issues of Embeded devices
Yasuyoshi Uemura
Define a few words, M2M, IoT, CPS, Embedded devices and so on
Secure Machine to Machine Authentication through IC chip in the microcomputer
Authentication between elements in the closed system
Authentication between elements in the open network
Authentication between Control part and Controlled part
Threats to devices, incidents and security
Managing vulnerabilities, from experiences of smartcard society